Schrodinger's Network Location - Direct Access client is both inside and outside corporate network at the same time?!
I'm currently working from home and managed to get myself locked out of a PC (Long story involving Bitlocker). Only way out from this was to re-install Windows and then rejoin to the domain.
Re-install is easy as I have WDS configured on my home network. Re-joining the domain is easy, I could either do an offline domain join with Direct Access policies embedded, or just connect the FortiGate VPN and join the domain and run gpupdate. I went with the latter as it seemed like it'd be the easier option. As I'd used WDS, the PC was now part of my home network domain, so I removed it from the domain, renamed and rebooted. I then went and connected it to the work domain and ran gpupdate, all fine, and restarted the PC. That's when it got weird.
So the PC boots up and I can log in with any domain credentials fine. Once logged on I realise I can't access any network resources, and a look on the Remote Access console on the server running Direct Access shows that nothing has connected. Odd how it could log me on though, with fresh credentials that had never logged on before? I tried a few test accounts and it let those log in too...
A lot of troubleshooting later I discovered it establishing a connection during bootup then dropping it, and errors appearing in the System log about an IPv6 interface not establishing properly.
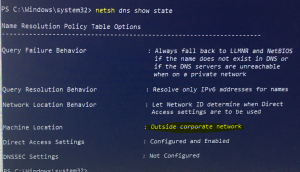
I went through the usual Direct Access troubleshooting: - netsh namespace show effectivepolicy - all appearing as it should - netsh dns show state - this said I was outside the corporate network - Get-DAConnectionStatus - this said I was connected locally, as does the Windows Settings UI.
Hold on, how can I be outside the network and connected locally at the same time? I can't resolve the NLS server address - if this is resolvable it means I'm connected locally, if not resolvable I must be working remotely.
I then ran netsh advfirewall monitor show mmsa and nothing came up. There's usually two entries there when it's connected up properly.
Very odd. I then compared all the above to the output from a laptop which was connecting to Direct Access without issues. All the same except Get-DAConnectionStatus was showing that it was connected remotely, and the firewall command was showing the two expected entries.
I then tried netsh interface httpstunnel show interface and I see the correct endpoint name and that it is connected. Odd. So I try pinging the 6to4 IP addresses of various hosts on the network (by trying to ping by hostname on a laptop which was connected to Direct Access, then copying the IPv6 address off screen). It was replying, how odd. But I couldn't access anything or resolve any addresses.
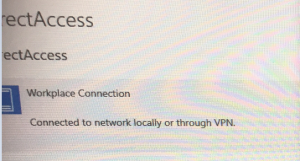
Finally I had a look in the old Network Connections screen (inside Control Panel rather than the new Settings one) and discover that the laptop, which is joined to the work domain but has never been joined to my home domain, has the LAN connection set as "Private Network". The PC which was on my domain, then removed and joined to the work domain still shows it as "Domain".
As far as I can recall the only way to change the network location is in the registry if the current location is Domain. (If it were private/public you can switch between the two via the UI). So I went into registry editor, then into the HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Profiles key. There were three keys (all with GUIDs as their name) for various networks (which appeared to all be my network). Once I'd deleted these three, disabled and re-enabled the NIC in the PC and given ncasvc service a restart it suddenly started working - Direct Access connected, it appeared in the console on the server, Get-DAConnectionStatus was reporting "ConnectedRemotely" and the firewall command was showing the two entries.
An hour wasted and I learnt that it doesn't matter about NLS, if your NIC thinks it's on the domain then Direct Access won't even attempt to connect!

