MEM: iOS Wireless Profile with embedded credentials
It's something that isn't recommended but sometimes there's not really much you can do otherwise - we have a set of iPad minis which are shared between multiple pupils and at the moment they are on Meraki MDM, connected to the 8021X Enterprise wireless network using a username/password which is set via the MDM profile. I really want to move these devices to Intune but you can't create a WiFi profile with embedded credentials on Intune - presumably this was never an option for obvious reasons.
The only other option I can see is to set up SCEP and have the devices issued with certificates, and then use those to authenticate, presumably I'd also need to enable device writeback so that the NPS server can see the devices in AD. Due to the way our AD is configured (single forest with lots of domains, synced to multiple Azure AD tenancies) device writeback is unsupported, so let's look at embedding the credentials into Intune instead.
Creating the AC2 Profile
When creating an iOS configuration profile on Intune we have the option to use a Custom one - where you just feed it the .mobileconfig XML file from Apple Configurator 2. I'm going to assume you're using an 802.1X Enterprise wireless network where the user authenticates against a RADIUS server such as NPS. So first think you'll need to do is find a mac with Apple Configurator 2 installed, and open it. Then go File > New Profile.
Fill out the General tab as this is mandatory - just put a profile name and configure whether you want the profile to be removable or not.
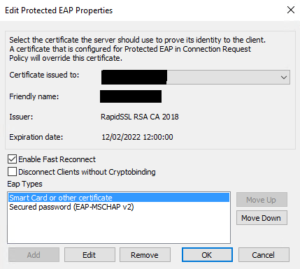
Next go to the Certificates tab, and add the certificate used by the NPS server. You can see what this is by opening NPS and going to Network Policies, then double-click the appropriate policy and go to the Constraints tab. Select "Microsoft: Protected EAP (PEAP)" and click Edit.
Once you've worked out which certificate it is using, you'll need to save the certificate - you can do this through opening mmc.exe and adding the Certificates snap-in (focussed on This Computer), find the certificate and export it. You just need the certificate itself as a .cer, you don't need the key and it doesn't need to be a PFX.
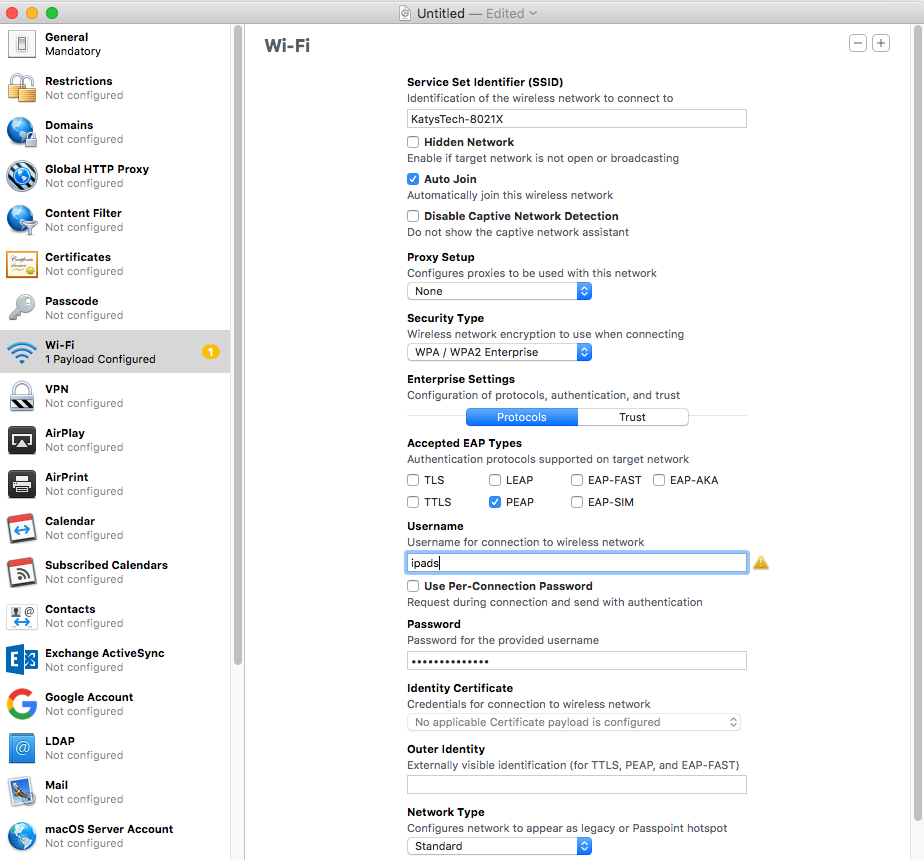
Now go to the WiFi tab and fill out the details - so in my case, the SSID, enabling Auto-Join and selecting WPA/WPA2 Enterprise as the security type. You'll then need to pick the Accepted EAP Type - for NPS it will be PEAP - and then on Certificates, tick the certificate you added earlier. If you skip adding the certificate and skip this step then the user will be prompted to trust the certificate when first connecting to the wireless network, which defeats the purpose of configuring it for them with a profile.
Next fill out the username and password used - in my case I have a shared account for shared iPads used only for connecting to the wireless network.
Finally click on File > Save and copy the .mobileconfig file somewhere you can access it from the Intune portal.
Importing the Profile to Intune
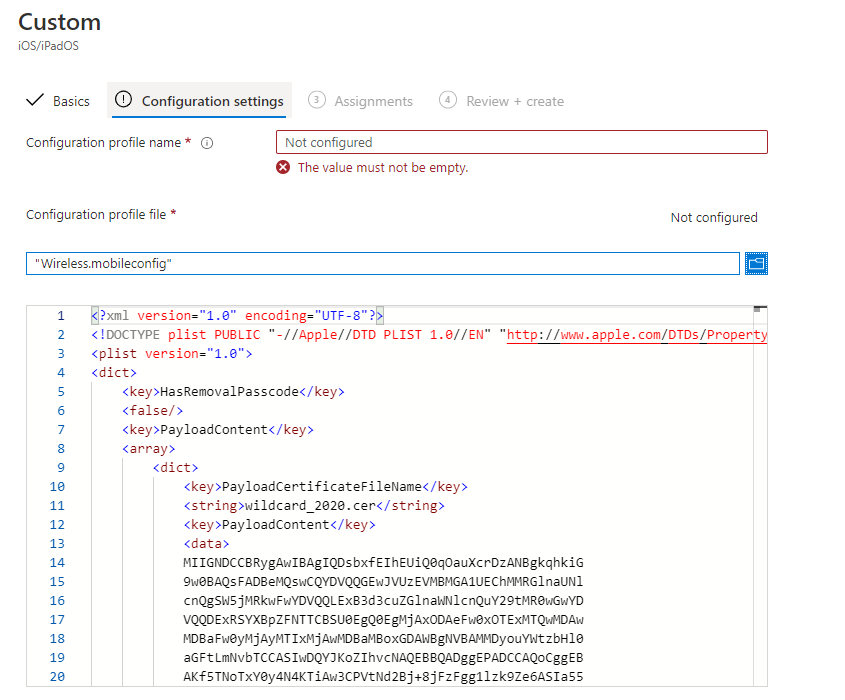
Now go to Intune > Devices > iOS/iPadOS > Configuration Profiles and click on Create Profile. Select Custom from the dropdown list of profile types.
Work through the screens setting the name etc on the Basics tab, then on Configuration Settings you'll need to enter the profile name, and click the browse icon to find the .mobileconfig file you made on Apple Configurator 2 earlier.
Finally assign the profile to the relevant device groups and finish.
Once your devices have synced you should find your wireless network has been added, with the stored credentials, and it should connect automatically with no prompts, although you may need to remove it from the existing wireless network manually.

