Intune: Windows Hello for Business

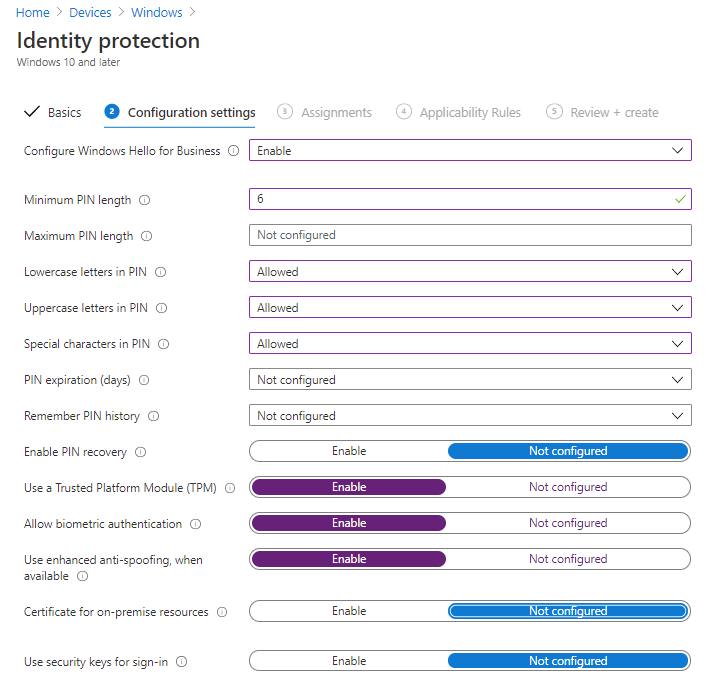
Windows Hello is Windows 10's biometric authentication system which allows users to sign into their device using facial recognition (if the device has an IR camera), fingerprint (if the device has a fingerprint reader) and PIN. The data for these is stored on the device itself rather than transmitted to the authentication provider (i.e. Azure AD) so is more secure than a password as an attacker would need the device as well as the face/finger/PIN of the person they are trying to impersonate. In this case a PIN is more like a password, as we can define the minimum and maximum length, and allow/forbid/require lower case, upper case and special characters. The default setting permits numbers, lower and upper case letters but does not allow special characters.
At a basic level it works by using a public/private key pair or certificate based authentication. The private key and other biometric data is stored in the device, either in the TPM chip (if present) or in the file system. Windows Hello for Business is the enterprise version of Windows Hello and can be configured using Group Policy or a modern MDM such as Intune.
If configured correctly it can also be used to authenticate to on-premise resources such as from a domain-joined or hybrid-joined device. My preferred method of working here is to move things to use modern authentication and as such the devices I use to test this are just Azure AD joined (and provisioned using Autopilot), so I won't be setting up the certificate for on-premise authentication. If you want to read more about configuring Windows Hello for Business SSO to on-premise resources, I have posted recently about this.
Create a Configuration Profile
First of all we need to go to Intune > Devices > Configuration Profiles and click Create profile. Select Windows 10 and later platform and Identity protection profile type.
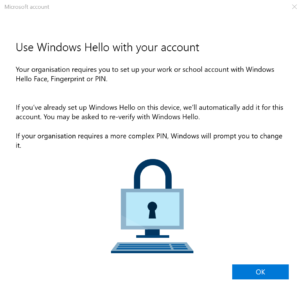
Then assign it to your device group. Once a user has logged on to one of the devices they will have to wait for the profile to apply to their user account, when I've tested this it didn't take too long on a fresh device but took a while on one that hadn't been powered on for a few weeks. You can monitor this in the Intune portal by going into your configuration profile and looking at Device status.
Testing
When I tried this I was getting some failures reported on applying the profile when nobody was logged on, but once a user had logged on it was applying the profile to them fine. Now all the user needs to do is open Windows 10 Settings > Accounts > Sign-in Options and turn on the desired Windows Hello settings:
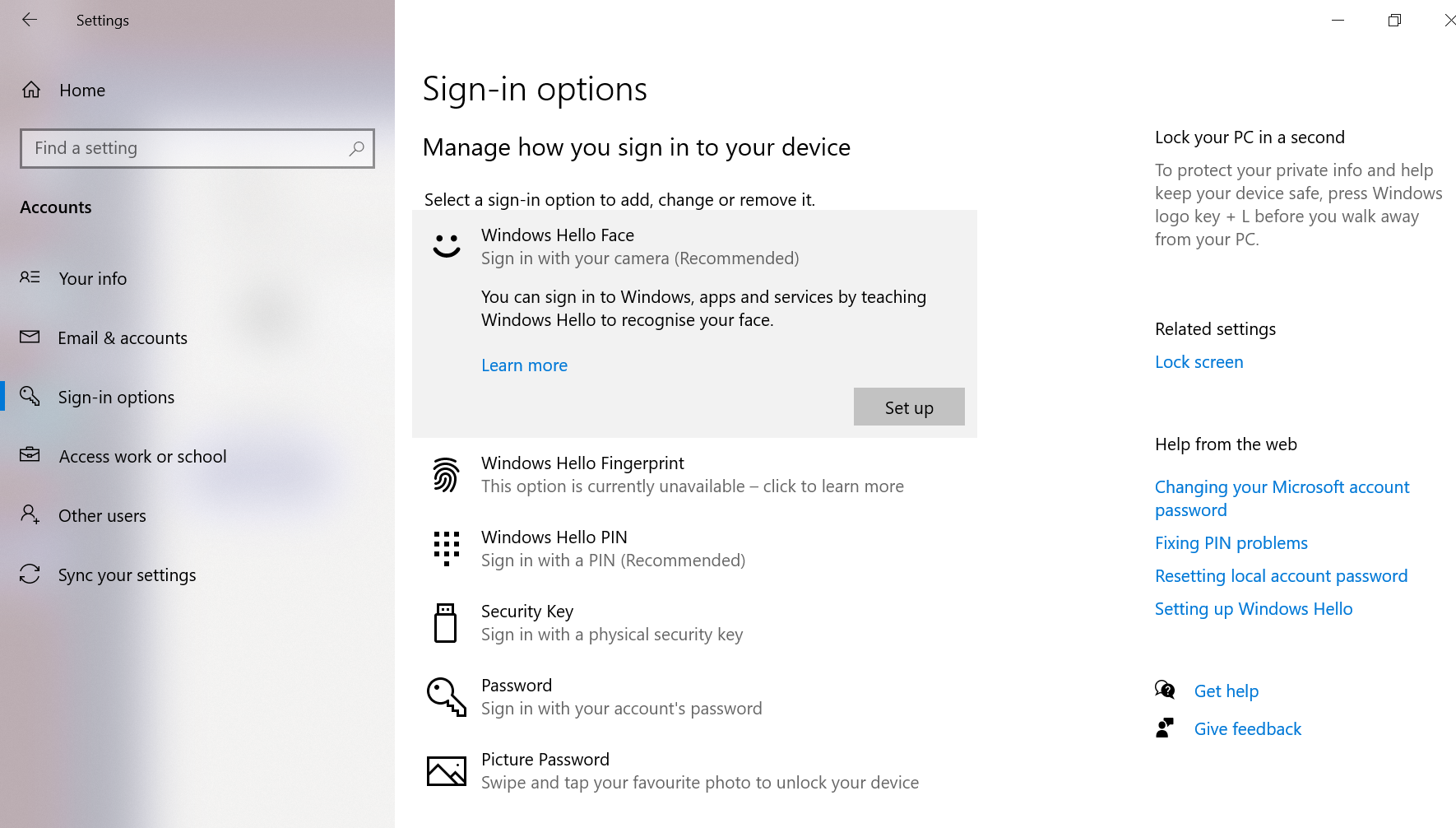
I was using a Surface Go to write this so don't have the ability to try fingerprint logon but I could set up Face logon. The user is required to also set a PIN incase something goes wrong with Face logon - this has to follow the rules set out when we defined the profile in Intune. Once done they can log on by looking at the camera, neat.
This only works on the specific device they are using as it creates a public/private key pair and stores the private key in the device's TPM chip, or in the file system if there is no TPM chip present. They will need to configure Windows Hello on each device they want to use it with.
Further Reading
- How Windows Hello for Business works - Microsoft 365 Security | Microsoft Docs
- Windows Hello for Business settings in Microsoft Intune - Azure | Microsoft Docs
- Use a PIN to sign in to Windows 10 devices using Microsoft Intune - Azure | Microsoft Docs
- Azure AD and Windows Hello: SSO to on-premise resources

