Intune: Setting Client Registry Keys
With domain joined clients we've been able to push out registry setting changes with things like Group Policy Preferences. Unfortunately there isn't an equivalent to this in MEM. While your best plan here would be to find the setting within the Settings Catalog or Templates in a configuration profile, or even look for an OMA-URI which can be set, there will always be some tasks which can only be achieved by directly setting a registry key.
Within MEM we can create PowerShell scripts which run once per user/device. We can specify whether we want these to run in user context or system context. The scripts are downloaded to the device by the Intune Management Extension (IME) and run once per user. If the script is running under the system context then the user does not need to be logged in for the script to execute. If you update the script, it will run again. If it is set to run in user context, and the user is a local administrator, it will run with administrative privileges.
This seems perfect for any registry keys we may wish to change once only. We can of course use Proactive Remediation instead (part of Endpoint Analytics, mentioned briefly in this post however I do plan a detailed look at Proactive Remediation soon) which would allow us to schedule the script to run frequently, as a detect/remediate script pair.
So the first thing we'll need to do is prepare a PowerShell script. The script below, purely as an example - as there's most likely a CSP setting for this - will set the 'Licence to' name within Windows:
Set-ItemProperty -Path "HKLM:\SOFTWARE\Microsoft\Windows NT\CurrentVersion" -Name RegisteredOwner -Value "Katy Nicholson"
Save the script, then go to Devices > Scripts in the MEM portal and add a new script. Fill out the Basics screen with a name and optional description, then upload your script on the Script Settings page.
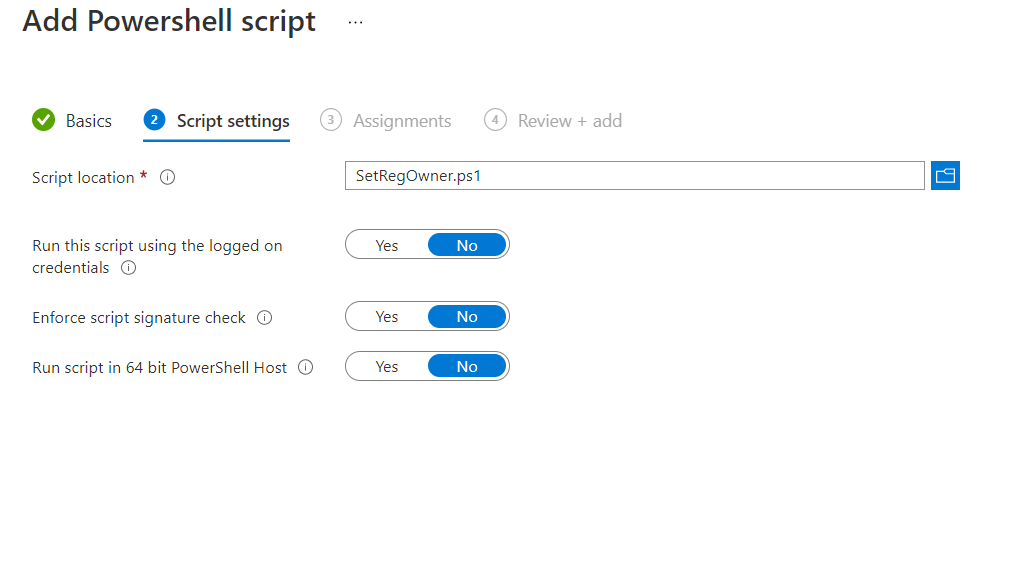
As with Proactive Remediation scripts, we get some similar options here:
- Run this script using the logged on credentials: As it says. Yes to run as user context, No for system.
- Enforce script signature check: There are no popups or prompts to the user when a script runs through IME. If you enforce signature checks, your script needs to be correctly signed and valid.
- Run script in 64 bit PowerShell Host: By default the script runs in the 32 bit PowerShell host.
Finally, on the Assignments screen, assign to users/devices in the usual manner.
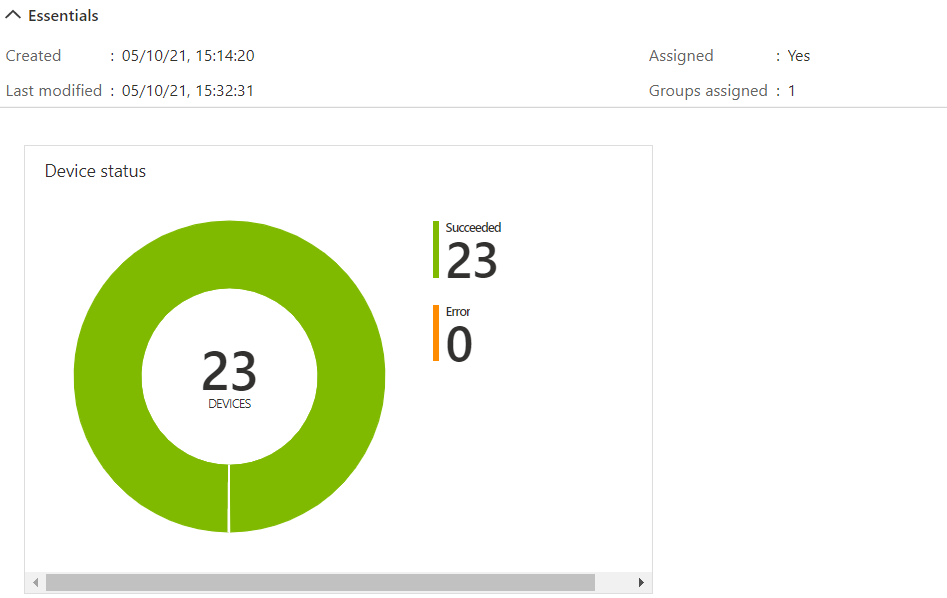
Once it has rolled out across your devices you'll be able to see some feedback as to how many devices/users it has run for, whether they were successful or not. You can also go into further detail and get a complete list of devices and user/device pairs.